The New Frontline in Cybersecurity
In the evolving landscape of cybersecurity, the recent apprehension of a former Google engineer for illicitly sharing AI technology secrets underscores a pervasive threat: the malicious insider. This incident not only highlights the fragility of trust within organizations but also serves as a stark reminder of the critical role cyberculture plays in safeguarding intellectual property. As businesses grapple with the complexities of human risk management, this revelation prompts a deeper exploration into the strategies that foster a robust cybersecurity awareness, emphasizing the need for a proactive and inclusive approach to mitigating insider threats.
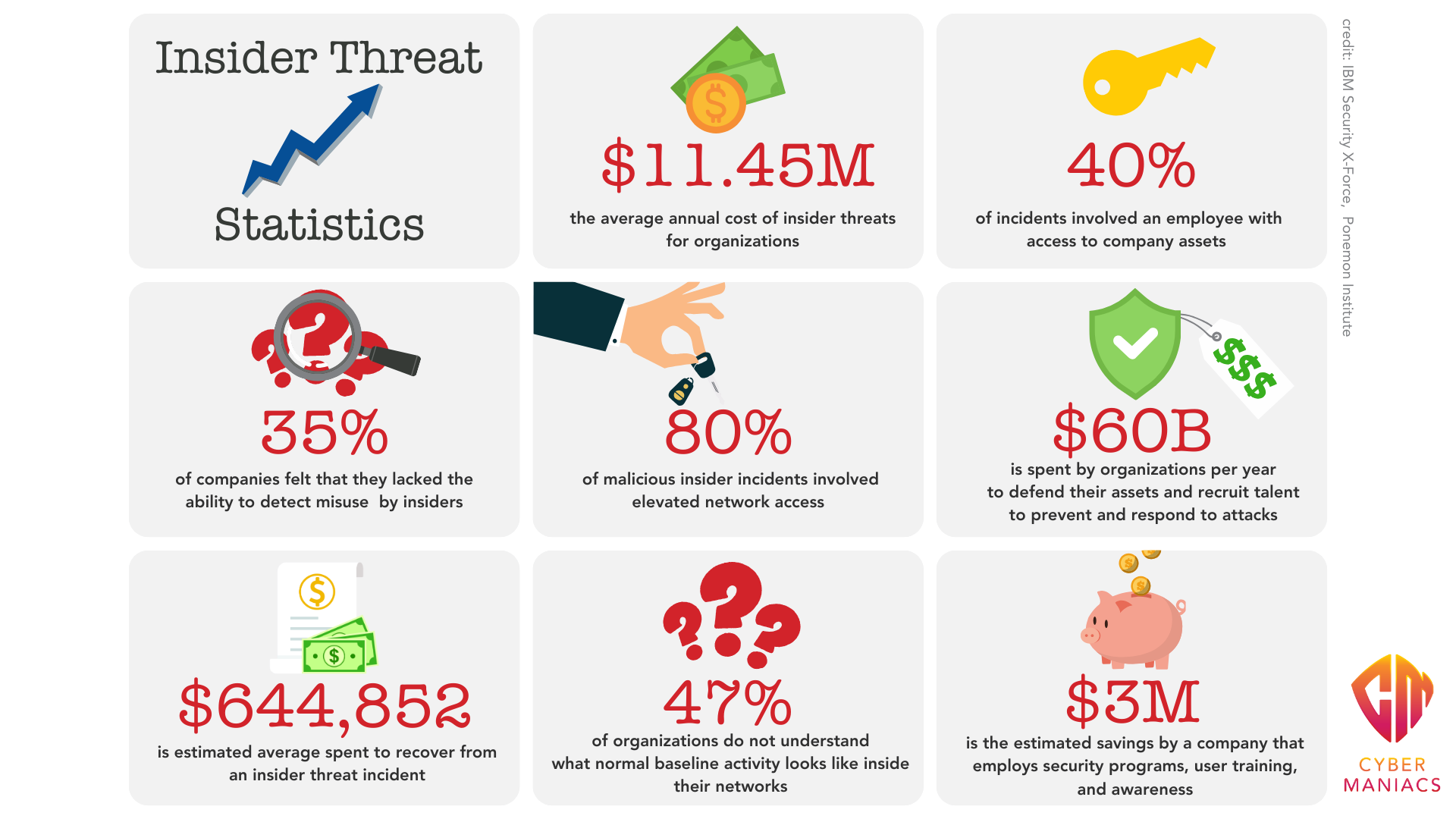
The Cost of Complacency: A Cross-Industry Hazard
While the case of the Google Engineer is the most high-profile one, there cases of insider threats at Tesla and General Electric in the past few years illustrate the omnipresent danger of malicious insiders across various industries. Tesla’s ordeal with a former employee altering its source code and leaking proprietary data, alongside General Electric’s battle against economic espionage involving turbine technology, starkly reveals the extensive business risks tied to intellectual property theft. These incidents underscore the necessity for companies, especially those rich in IP, to adopt comprehensive cybersecurity awareness training and human risk management practices, thereby mitigating the potential for such detrimental breaches.
Beyond Training: The Crucial Role of Culture
While cybersecurity awareness training is a critical step toward safeguarding intellectual property, it alone is insufficient in the absence of a supportive and inclusive cyberculture. Traditional compliance-based once-a-year training programs and punitive phishing simulations, fail to fully address the nuanced human behaviors that contribute to insider threats. A mere focus on compliance measures overlooks the importance of understanding and mitigating human risk. To truly protect against malicious insiders, organizations must go beyond conventional training, fostering an environment where employees are not just informed but also genuinely engaged and invested in the collective security posture.
To construct a culture of security, actionable steps, and targeted questions are essential. Here's a detailed guide:
-
Conduct an Insider Threat Assessment
- What are our critical assets? Who has access to these assets?
- Actions to Take: Map out critical data flows within your organization. Identify potential insider threat profiles based on access and privilege levels.
- Engage in a Culture Audit and Human Risk Assessment
- How do employees perceive our cyber culture? Are they comfortable reporting suspicious behavior? Where does human risk predominantly lie within our organization?
- Actions to take: Utilize anonymous surveys to gauge the current state of your cyberculture, such as our Human Cyber Baseline Assessment.
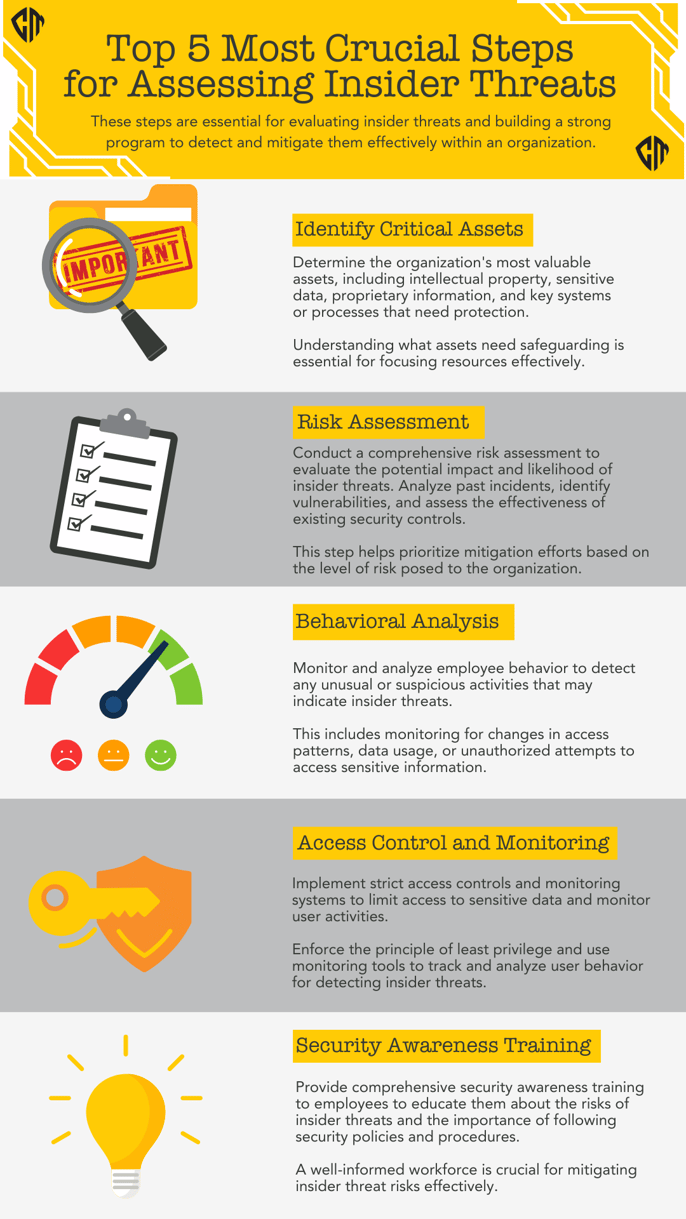
- Identify Key IP Areas ("Crown Jewels")
- What data, if lost, would significantly impact our business? Chances are, there are many different kinds. If your DPO doesn’t have this and you haven’t mapped to roles, culture, behavior, and risk metrics, this is the year to do so.
- Actions to Take: Catalog and prioritize your IP in terms of confidentiality, integrity, and availability requirements. Map to roles and the learning objectives in your training and awareness program. (Not sure how to do this? We can show you how.)
- Analyze Roles and Access
- Do employees have access to information beyond their job requirements? How is access granted and reviewed?
- Actions to Take: Implement a principle of least privilege. Regularly review and adjust access rights as roles or projects change.
By addressing these areas with thoughtful questions and concrete steps, organizations can enhance their cybersecurity posture from the inside out, creating a more secure and resilient environment against insider threats.
Empowering Employees: Overcoming Psychological Barriers
Understanding the cyberpsychology of an organization involves recognizing the underlying behaviors, attitudes, and emotions that influence cybersecurity practices. Initially, assess the overall awareness and attitude towards cybersecurity across the organization. This assessment can reveal areas where friction, challenges, or resistance may arise, such as reluctance to adopt new security measures, skepticism towards the effectiveness of training, or discomfort in reporting suspicious activities.
To address these challenges:
- Encourage Open Dialogue: Create forums for employees to express concerns and suggestions about cybersecurity practices.
- Tailor Awareness Programs: Develop training that resonates with different employee demographics and roles, acknowledging their unique perspectives and challenges.
- Promote Psychological Safety: Foster an environment where employees feel safe to report incidents without fear of blame or retribution.
- Recognize and Address Resistance: Understand the root causes of pushback against cybersecurity policies and work towards solutions that minimize discomfort while maximizing security.
By focusing on the human factors that influence cybersecurity, organizations can cultivate a culture that supports vigilant, cyber-safe behaviors.
Towards a Culture of Trust and Vigilance
In navigating the complex landscape of insider threats, it's clear that fostering a robust cyberculture built on trust, openness, and mutual respect is paramount. Organizations must look beyond traditional security measures to understand the intricate web of human risk management. By engaging in comprehensive culture audits, fostering environments that encourage speaking up without fear, and tailoring cybersecurity practices to address psychological barriers, companies can create a resilient defense against both external and internal threats. Let's commit to a future where cybersecurity is not just about technology but about cultivating a culture that champions security as a shared responsibility.





